packj github action
1.0.0
将packj添加到您的工作流程中,以审核您的破坏/风险npm/pypi/ruby依赖性的拉动请求。
由我们的开源工具PackJ提供动力。
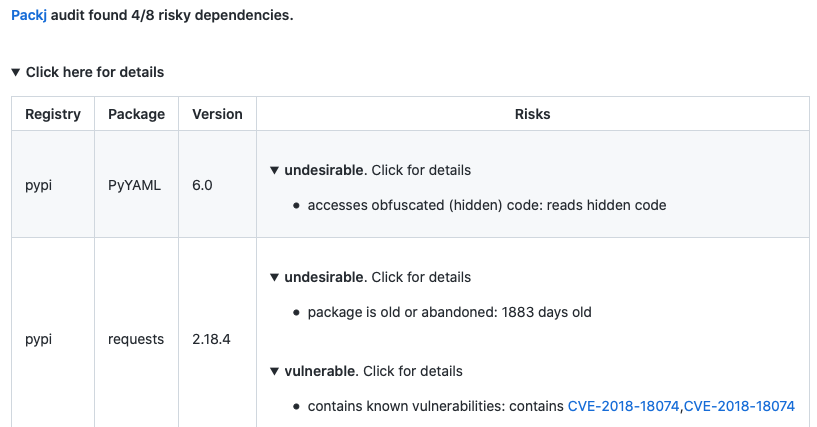
如果发现任何风险依赖性,Packj将对PR发表评论。请参阅示例拉请求审核。
只需将以下内容添加到您的工作流程中:
- name : Packj Security Audit
uses : ossillate-inc/[email protected]
with :
# TODO: replace with your dependency files in the repo
DEPENDENCY_FILES : pypi:requirements.txt,npm:package.json,rubygems:Gemfile
REPO_TOKEN : ${{ secrets.GITHUB_TOKEN } # This is a basic workflow to help you get started with Actions
name : Packj security audit
# Controls when the workflow will run
on :
pull_request :
branches :
- main
# A workflow run is made up of one or more jobs that can run sequentially or in parallel
jobs :
# This workflow contains a single job called "packj-audit"
packj-security-audit :
# The type of runner that the job will run on
runs-on : ubuntu-latest
# Steps represent a sequence of tasks that will be executed as part of the job
steps :
# Audit
- name : Audit dependencies
uses : ossillate-inc/[email protected]
with :
# TODO: replace with your dependency files in the repo
DEPENDENCY_FILES : pypi:requirements.txt,npm:package.json,rubygems:Gemfile
REPO_TOKEN : ${{ secrets.GITHUB_TOKEN }}secrets.GITHUB_TOKEN默认使用(github Action Runner)false 。PackJ可以审核PYPI,NPM和RubyGems软件包。它执行:
connect , exec ),open() , fork() ),以检查软件包(和所有依赖关系)的运行时行为。出于安全原因,具有过期电子邮件域,较大的发布时间差距,敏感API等的软件包被标记为风险。
PackJ的设计取决于我们对651个已记录的开源软件供应链攻击的恶意软件样本的研究。它扫描了40多种风险代码和元数据属性,这些属性使一个包裹易受供应链攻击的影响。
| 风险 | 原因 |
|---|---|
| 冒充流行包裹的包装 | 不良演员通过出版的恶意软件包进行了错字攻击,这些攻击是模仿流行套餐的(例如,lodash vs loadash) |
| 旧的或放弃的包裹 | 旧的或未经最终的软件包未收到安全修复程序 |
| 使用敏感API的软件包,例如EXEC和EDAR | 恶意软件使用操作系统或语言运行时的API来执行敏感操作(例如,读取SSH键) |
| 贡献者的包裹无效或没有电子邮件地址 | 错误或丢失的电子邮件地址表明该帐户缺少2FA,这使得不良演员更容易劫持所有权。 |
| 无效或没有公共源存储库的软件包 | 没有公共回购意味着公开审核或审查源代码的简单方法 |
| 包含已知漏洞的软件包 | 软件包代码中已知的安全漏洞(CVE)可以由坏参与者利用 |
可以自定义PackJ,以仅发送适用于威胁模型的警报。只需根据我们的模板(下图)在您的存储库中添加.packj.yaml文件,然后启用/禁用对您重要的警报即可。
# # Audit policies # audit: # # Risk alerts (enable or disable according to your threat model) # alerts: # # category: malicious packages (publicly known and unknown) # malicious: contains known malware: - reason: package is known to contain a dangerous malware - enabled: true typo-squatting or repo-jacking package: - reason: package impersonates another popular package to propagate malware - enabled: true # # alert category: packages vulnerable to code exploits # vulnerable: contains known vulnerabilities: - reason: known vulnerabilities (CVEs) in package code could be exploited - enabled: true # # packages with undesirable or "risky" attributes # undesirable: package is old or abandoned: - reason: old or abandoned packages receive no security updates and are risky - enabled: true invalid or no author email: - reason: a package with lack of or invalid author email suggests 2FA not enabled - enabled: true invalid or no homepage: - reason: a package with no or invalid homepage may not be preferable - enabled: false no source repo: - reason: lack of public source repo may suggest malicious intention - enabled: true fewer downloads: - reason: a package with few downloads may not be preferable - enabled: true no or insufficient readme: - reason: a package with lack of documentation may not be preferable - enabled: false fewer versions or releases: - reason: few versions suggest unstable or inactive project - enabled: true too many dependencies: - reason: too many dependencies increase attack surface - enabled: false version release after a long gap: - reason: a release after a long time may indicate account hijacking - enabled: false contains custom installation hooks: - reason: custom installation hooks may download or execute malicious code - enabled: false # WIP # # type: repo stats # few source repo stars: - reason: a package with few repo stars may not be preferable - enabled: false few source repo forks: - reason: a package with few repo forks may not be preferable - enabled: false forked source repo: - reason: a forked copy of a popular package may contain malicious code - enabled: true # # type: APIs and permissions # generates new code: - reason: package generates new code at runtime, which could be malicious - enabled: false forks or exits OS processes: - reason: package spawns new operating system processes, which could be malicious - enabled: false accesses obfuscated (hidden) code: - enabled: true accesses environment variables: - enabled: false changes system/environment variables: - enabled: false accesses files and dirs: - enabled: false communicates with external network: - enabled: false reads user input: - enabled: false sandbox: rules: # # File system (allow or block accesses to file/dirs) # # ~/ represents home dir # . represents cwd dir # # NOTE: only ONE 'allow' and 'block' lines are allowed # fs: # TODO: customize as per your threat model # block access to home dir and all other locations (except the ones below) block: ~/, / allow: ., ~/.cache, ~/.npm, ~/.local, ~/.ruby, /tmp, /proc, /etc, /var, /bin, /usr/include, /usr/local, /usr/bin, /usr/lib, /usr/share, /lib # # Network (allow or block domains/ports) # # NOTE: only ONE 'allow' and 'block' lines are allowed # network: # TODO: customize as per your threat model # block all external network communication (except the ones below) block: 0.0.0.0 # For installing PyPI, Rubygems, and NPM packages allow: pythonhosted.org:443, pypi.org:443, rubygems.org:443, npmjs.org:0, npmjs.com:0