Adicione o PackJ ao seu fluxo de trabalho para auditar suas solicitações de tração para dependências maliciosas/arriscadas de NPM/PYPI/Ruby.
Alimentado por nosso pacote de ferramentas de código aberto.
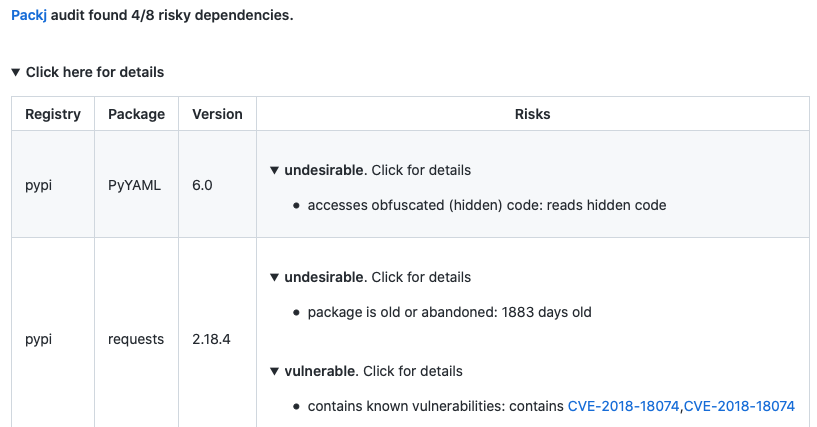
PackJ comentará o PR se alguma dependência arriscada for encontrada. Consulte Exemplo Pull Request Audit.
Basta adicionar o seguinte ao seu fluxo de trabalho:
- name : Packj Security Audit
uses : ossillate-inc/[email protected]
with :
# TODO: replace with your dependency files in the repo
DEPENDENCY_FILES : pypi:requirements.txt,npm:package.json,rubygems:Gemfile
REPO_TOKEN : ${{ secrets.GITHUB_TOKEN } # This is a basic workflow to help you get started with Actions
name : Packj security audit
# Controls when the workflow will run
on :
pull_request :
branches :
- main
# A workflow run is made up of one or more jobs that can run sequentially or in parallel
jobs :
# This workflow contains a single job called "packj-audit"
packj-security-audit :
# The type of runner that the job will run on
runs-on : ubuntu-latest
# Steps represent a sequence of tasks that will be executed as part of the job
steps :
# Audit
- name : Audit dependencies
uses : ossillate-inc/[email protected]
with :
# TODO: replace with your dependency files in the repo
DEPENDENCY_FILES : pypi:requirements.txt,npm:package.json,rubygems:Gemfile
REPO_TOKEN : ${{ secrets.GITHUB_TOKEN }}secrets.GITHUB_TOKEN é usado por padrão (github Action Runner)false .O PackJ pode auditar os pacotes Pypi, NPM e Rubygems . Ele executa:
connect , exec ),open() , fork() ).Pacotes com domínios de email vencidos, grande lacuna no tempo de liberação, APIs sensíveis etc. são sinalizadas como arriscadas por razões de segurança.
O design do PackJ é guiado por nosso estudo de 651 amostras de malware de ataques documentados da cadeia de suprimentos de software de código aberto. Ele digitaliza mais de 40 atributos de código de risco e metadados que tornam um pacote vulnerável a ataques da cadeia de suprimentos.
| Risco | Razão |
|---|---|
| Pacotes representando pacotes populares | Os maus atores realizam ataques de digitação de digitação da publicação de pacotes maliciosos que personalizam pacotes populares (por exemplo, lodash vs loadash) |
| Pacotes antigos ou abandonados | Pacotes antigos ou não mantidos não recebem correções de segurança |
| Pacote usando APIs sensíveis, como EXEC e avaliação | Malware usa APIs do sistema operacional ou tempo de execução da linguagem para executar operações sensíveis (por exemplo, Leia as teclas SSH) |
| Pacotes com endereços inválidos ou nenhum e -mail dos colaboradores | Endereços de e -mail incorretos ou ausentes sugerem falta de 2FA na conta, o que facilita para os maus atores sequestrar a propriedade do pacote |
| Pacotes com repositório inválido ou sem fonte pública | Ausência de um repositório público não significa maneira fácil de auditar ou revisar o código -fonte publicamente |
| Pacotes que contêm vulnerabilidades conhecidas | As vulnerabilidades de segurança conhecidas (CVEs) no código do pacote podem ser exploradas por maus atores |
O PackJ pode ser personalizado para enviar apenas alertas que se aplicam ao seu modelo de ameaça. Basta adicionar um arquivo .packj.yaml no seu repositório com base no nosso modelo (abaixo) e ativar/desativar alertas que importam para você.
# # Audit policies # audit: # # Risk alerts (enable or disable according to your threat model) # alerts: # # category: malicious packages (publicly known and unknown) # malicious: contains known malware: - reason: package is known to contain a dangerous malware - enabled: true typo-squatting or repo-jacking package: - reason: package impersonates another popular package to propagate malware - enabled: true # # alert category: packages vulnerable to code exploits # vulnerable: contains known vulnerabilities: - reason: known vulnerabilities (CVEs) in package code could be exploited - enabled: true # # packages with undesirable or "risky" attributes # undesirable: package is old or abandoned: - reason: old or abandoned packages receive no security updates and are risky - enabled: true invalid or no author email: - reason: a package with lack of or invalid author email suggests 2FA not enabled - enabled: true invalid or no homepage: - reason: a package with no or invalid homepage may not be preferable - enabled: false no source repo: - reason: lack of public source repo may suggest malicious intention - enabled: true fewer downloads: - reason: a package with few downloads may not be preferable - enabled: true no or insufficient readme: - reason: a package with lack of documentation may not be preferable - enabled: false fewer versions or releases: - reason: few versions suggest unstable or inactive project - enabled: true too many dependencies: - reason: too many dependencies increase attack surface - enabled: false version release after a long gap: - reason: a release after a long time may indicate account hijacking - enabled: false contains custom installation hooks: - reason: custom installation hooks may download or execute malicious code - enabled: false # WIP # # type: repo stats # few source repo stars: - reason: a package with few repo stars may not be preferable - enabled: false few source repo forks: - reason: a package with few repo forks may not be preferable - enabled: false forked source repo: - reason: a forked copy of a popular package may contain malicious code - enabled: true # # type: APIs and permissions # generates new code: - reason: package generates new code at runtime, which could be malicious - enabled: false forks or exits OS processes: - reason: package spawns new operating system processes, which could be malicious - enabled: false accesses obfuscated (hidden) code: - enabled: true accesses environment variables: - enabled: false changes system/environment variables: - enabled: false accesses files and dirs: - enabled: false communicates with external network: - enabled: false reads user input: - enabled: false sandbox: rules: # # File system (allow or block accesses to file/dirs) # # ~/ represents home dir # . represents cwd dir # # NOTE: only ONE 'allow' and 'block' lines are allowed # fs: # TODO: customize as per your threat model # block access to home dir and all other locations (except the ones below) block: ~/, / allow: ., ~/.cache, ~/.npm, ~/.local, ~/.ruby, /tmp, /proc, /etc, /var, /bin, /usr/include, /usr/local, /usr/bin, /usr/lib, /usr/share, /lib # # Network (allow or block domains/ports) # # NOTE: only ONE 'allow' and 'block' lines are allowed # network: # TODO: customize as per your threat model # block all external network communication (except the ones below) block: 0.0.0.0 # For installing PyPI, Rubygems, and NPM packages allow: pythonhosted.org:443, pypi.org:443, rubygems.org:443, npmjs.org:0, npmjs.com:0