Tambahkan PackJ ke alur kerja Anda untuk mengaudit permintaan tarik Anda untuk dependensi NPM/PYPI/Ruby yang berbahaya/berisiko.
Didukung oleh paket alat open-source kami.
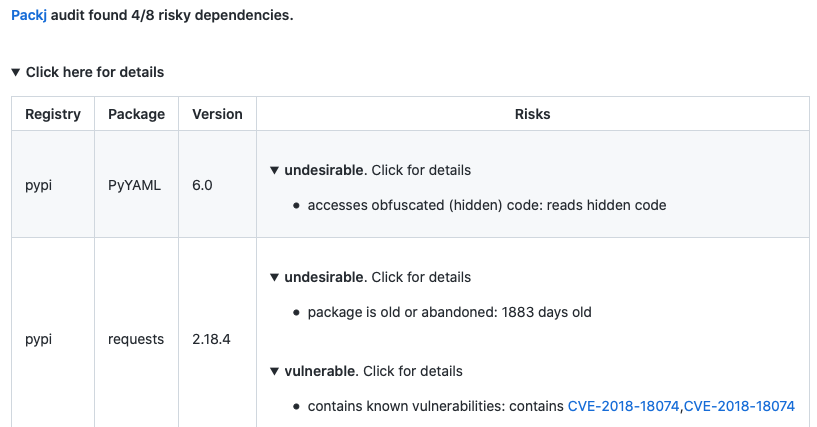
PackJ akan mengomentari PR jika ada dependensi berisiko. Lihat Contoh Audit Permintaan Tarik.
Cukup tambahkan yang berikut ini ke alur kerja Anda:
- name : Packj Security Audit
uses : ossillate-inc/[email protected]
with :
# TODO: replace with your dependency files in the repo
DEPENDENCY_FILES : pypi:requirements.txt,npm:package.json,rubygems:Gemfile
REPO_TOKEN : ${{ secrets.GITHUB_TOKEN } # This is a basic workflow to help you get started with Actions
name : Packj security audit
# Controls when the workflow will run
on :
pull_request :
branches :
- main
# A workflow run is made up of one or more jobs that can run sequentially or in parallel
jobs :
# This workflow contains a single job called "packj-audit"
packj-security-audit :
# The type of runner that the job will run on
runs-on : ubuntu-latest
# Steps represent a sequence of tasks that will be executed as part of the job
steps :
# Audit
- name : Audit dependencies
uses : ossillate-inc/[email protected]
with :
# TODO: replace with your dependency files in the repo
DEPENDENCY_FILES : pypi:requirements.txt,npm:package.json,rubygems:Gemfile
REPO_TOKEN : ${{ secrets.GITHUB_TOKEN }}secrets.GITHUB_TOKEN digunakan secara default (github action runner)false .PackJ dapat mengaudit paket PYPI, NPM, dan Rubygems . Itu melakukan:
connect , exec ),open() , fork() ).Paket dengan domain email yang sudah kadaluwarsa, kesenjangan waktu rilis besar, API sensitif, dll. Ditandai sebagai berisiko untuk alasan keamanan.
Desain PackJ dipandu oleh penelitian kami terhadap 651 sampel malware dari serangan rantai pasokan perangkat lunak open-source yang terdokumentasi. Ini memindai 40+ kode berisiko dan atribut metadata yang membuat paket rentan terhadap serangan rantai pasokan.
| Mempertaruhkan | Alasan |
|---|---|
| Paket Menyampaikan Paket Populer | Aktor buruk melakukan serangan kesalahan ketik dengan menerbitkan paket jahat yang menyamar sebagai paket populer (misalnya, Lodash vs Loadash) |
| Paket tua atau ditinggalkan | Paket lama atau tidak terawat tidak menerima perbaikan keamanan |
| Paket menggunakan API sensitif, seperti exec dan eval | Malware menggunakan API dari sistem operasi atau runtime bahasa untuk melakukan operasi sensitif (misalnya, baca tombol SSH) |
| Paket dengan alamat email yang tidak valid atau tidak | Alamat email yang salah atau hilang menunjukkan kurangnya 2FA di akun, yang memudahkan aktor buruk untuk membajak kepemilikan paket paket |
| Paket dengan Repo Sumber Publik Tidak Valid atau Tanpa Publik | Tidak adanya repo publik berarti tidak ada cara mudah untuk mengaudit atau meninjau kode sumber secara publik |
| Paket yang mengandung kerentanan yang diketahui | Kerentanan Keamanan yang Dikenal (CVE) dalam kode paket dapat dieksploitasi oleh aktor jahat |
PackJ dapat disesuaikan untuk hanya mengirim peringatan yang berlaku untuk model ancaman Anda. Cukup tambahkan file .packj.yaml di repo Anda berdasarkan templat kami (di bawah) dan aktifkan/nonaktifkan peringatan yang penting bagi Anda.
# # Audit policies # audit: # # Risk alerts (enable or disable according to your threat model) # alerts: # # category: malicious packages (publicly known and unknown) # malicious: contains known malware: - reason: package is known to contain a dangerous malware - enabled: true typo-squatting or repo-jacking package: - reason: package impersonates another popular package to propagate malware - enabled: true # # alert category: packages vulnerable to code exploits # vulnerable: contains known vulnerabilities: - reason: known vulnerabilities (CVEs) in package code could be exploited - enabled: true # # packages with undesirable or "risky" attributes # undesirable: package is old or abandoned: - reason: old or abandoned packages receive no security updates and are risky - enabled: true invalid or no author email: - reason: a package with lack of or invalid author email suggests 2FA not enabled - enabled: true invalid or no homepage: - reason: a package with no or invalid homepage may not be preferable - enabled: false no source repo: - reason: lack of public source repo may suggest malicious intention - enabled: true fewer downloads: - reason: a package with few downloads may not be preferable - enabled: true no or insufficient readme: - reason: a package with lack of documentation may not be preferable - enabled: false fewer versions or releases: - reason: few versions suggest unstable or inactive project - enabled: true too many dependencies: - reason: too many dependencies increase attack surface - enabled: false version release after a long gap: - reason: a release after a long time may indicate account hijacking - enabled: false contains custom installation hooks: - reason: custom installation hooks may download or execute malicious code - enabled: false # WIP # # type: repo stats # few source repo stars: - reason: a package with few repo stars may not be preferable - enabled: false few source repo forks: - reason: a package with few repo forks may not be preferable - enabled: false forked source repo: - reason: a forked copy of a popular package may contain malicious code - enabled: true # # type: APIs and permissions # generates new code: - reason: package generates new code at runtime, which could be malicious - enabled: false forks or exits OS processes: - reason: package spawns new operating system processes, which could be malicious - enabled: false accesses obfuscated (hidden) code: - enabled: true accesses environment variables: - enabled: false changes system/environment variables: - enabled: false accesses files and dirs: - enabled: false communicates with external network: - enabled: false reads user input: - enabled: false sandbox: rules: # # File system (allow or block accesses to file/dirs) # # ~/ represents home dir # . represents cwd dir # # NOTE: only ONE 'allow' and 'block' lines are allowed # fs: # TODO: customize as per your threat model # block access to home dir and all other locations (except the ones below) block: ~/, / allow: ., ~/.cache, ~/.npm, ~/.local, ~/.ruby, /tmp, /proc, /etc, /var, /bin, /usr/include, /usr/local, /usr/bin, /usr/lib, /usr/share, /lib # # Network (allow or block domains/ports) # # NOTE: only ONE 'allow' and 'block' lines are allowed # network: # TODO: customize as per your threat model # block all external network communication (except the ones below) block: 0.0.0.0 # For installing PyPI, Rubygems, and NPM packages allow: pythonhosted.org:443, pypi.org:443, rubygems.org:443, npmjs.org:0, npmjs.com:0