功能•安装•用法•运行Naabu•配置•NMAP集成•CDN/WAF排除•Discord
Naabu是用GO编写的端口扫描工具,可让您以快速可靠的方式列举主机的有效端口。这是一个非常简单的工具,可以在主机/主机列表上快速syn/connect/udp扫描,并列出返回答复的所有端口。
naabu -h这将显示该工具的帮助。这是它支持的所有开关。
Usage :
naabu [flags]
Flags :
INPUT :
-host string[] hosts to scan ports for (comma-separated)
-list, -l string list of hosts to scan ports (file)
-exclude-hosts, -eh string hosts to exclude from the scan (comma-separated)
-exclude-file, -ef string list of hosts to exclude from scan (file)
PORT :
-port, -p string ports to scan (80,443, 100-200)
-top-ports, -tp string top ports to scan (default 100) [full,100,1000]
-exclude-ports, -ep string ports to exclude from scan (comma-separated)
-ports-file, -pf string list of ports to scan (file)
-port-threshold, -pts int port threshold to skip port scan for the host
-exclude-cdn, -ec skip full port scans for CDN/WAF (only scan for port 80,443)
-display-cdn, -cdn display cdn in use
RATE-LIMIT :
-c int general internal worker threads (default 25)
-rate int packets to send per second (default 1000)
UPDATE :
-up, -update update naabu to latest version
-duc, -disable-update-check disable automatic naabu update check
OUTPUT :
-o, -output string file to write output to (optional)
-j, -json write output in JSON lines format
-csv write output in csv format
CONFIGURATION :
-config string path to the naabu configuration file (default $HOME/.config/naabu/config.yaml)
-scan-all-ips, -sa scan all the IP's associated with DNS record
-ip-version, -iv string[] ip version to scan of hostname (4,6) - (default 4) (default ["4"])
-scan-type, -s string type of port scan (SYN/CONNECT) (default "c")
-source-ip string source ip and port (x.x.x.x:yyy - might not work on OSX)
-interface-list, -il list available interfaces and public ip
-interface, -i string network Interface to use for port scan
-nmap invoke nmap scan on targets (nmap must be installed) - Deprecated
- nmap-cli string nmap command to run on found results (example : -nmap-cli 'nmap -sV')
-r string list of custom resolver dns resolution (comma separated or from file)
-proxy string socks5 proxy (ip[:port] / fqdn[:port]
-proxy-auth string socks5 proxy authentication (username:password)
-resume resume scan using resume.cfg
-stream stream mode (disables resume, nmap, verify, retries, shuffling, etc)
-passive display passive open ports using shodan internetdb api
-irt, -input-read-timeout value timeout on input read (default 3m0s)
-no-stdin Disable Stdin processing
HOST-DISCOVERY :
-sn, -host-discovery Perform Only Host Discovery
- Pn, -skip-host-discovery Skip Host discovery (Deprecated : use -wn/-with-host-discovery instead)
-wn, -with-host-discovery Enable Host discovery
-ps, -probe-tcp-syn string[] TCP SYN Ping (host discovery needs to be enabled)
-pa, -probe-tcp-ack string[] TCP ACK Ping (host discovery needs to be enabled)
-pe, -probe-icmp-echo ICMP echo request Ping (host discovery needs to be enabled)
-pp, -probe-icmp-timestamp ICMP timestamp request Ping (host discovery needs to be enabled)
-pm, -probe-icmp-address-mask ICMP address mask request Ping (host discovery needs to be enabled)
-arp, -arp-ping ARP ping (host discovery needs to be enabled)
-nd, -nd-ping IPv6 Neighbor Discovery (host discovery needs to be enabled)
-rev-ptr Reverse PTR lookup for input ips
OPTIMIZATION :
-retries int number of retries for the port scan (default 3)
-timeout int millisecond to wait before timing out (default 1000)
-warm-up-time int time in seconds between scan phases (default 2)
-ping ping probes for verification of host
-verify validate the ports again with TCP verification
DEBUG :
-health-check, -hc run diagnostic check up
-debug display debugging information
-verbose, -v display verbose output
-no-color, -nc disable colors in CLI output
-silent display only results in output
-version display version of naabu
-stats display stats of the running scan (deprecated)
-si, -stats-interval int number of seconds to wait between showing a statistics update (deprecated) (default 5)
-mp, -metrics-port int port to expose naabu metrics on (default 63636)下载准备运行二进制 /码头机或与GO安装
注意:安装Naabu之前,请确保安装
libpcap库进行数据包捕获。
要在Linux上安装LibCap: sudo apt install -y libpcap-dev ,在Mac上: brew install libpcap
go install -v github.com/projectdiscovery/naabu/v2/cmd/naabu@latest要在目标上运行该工具,只需使用以下命令即可。
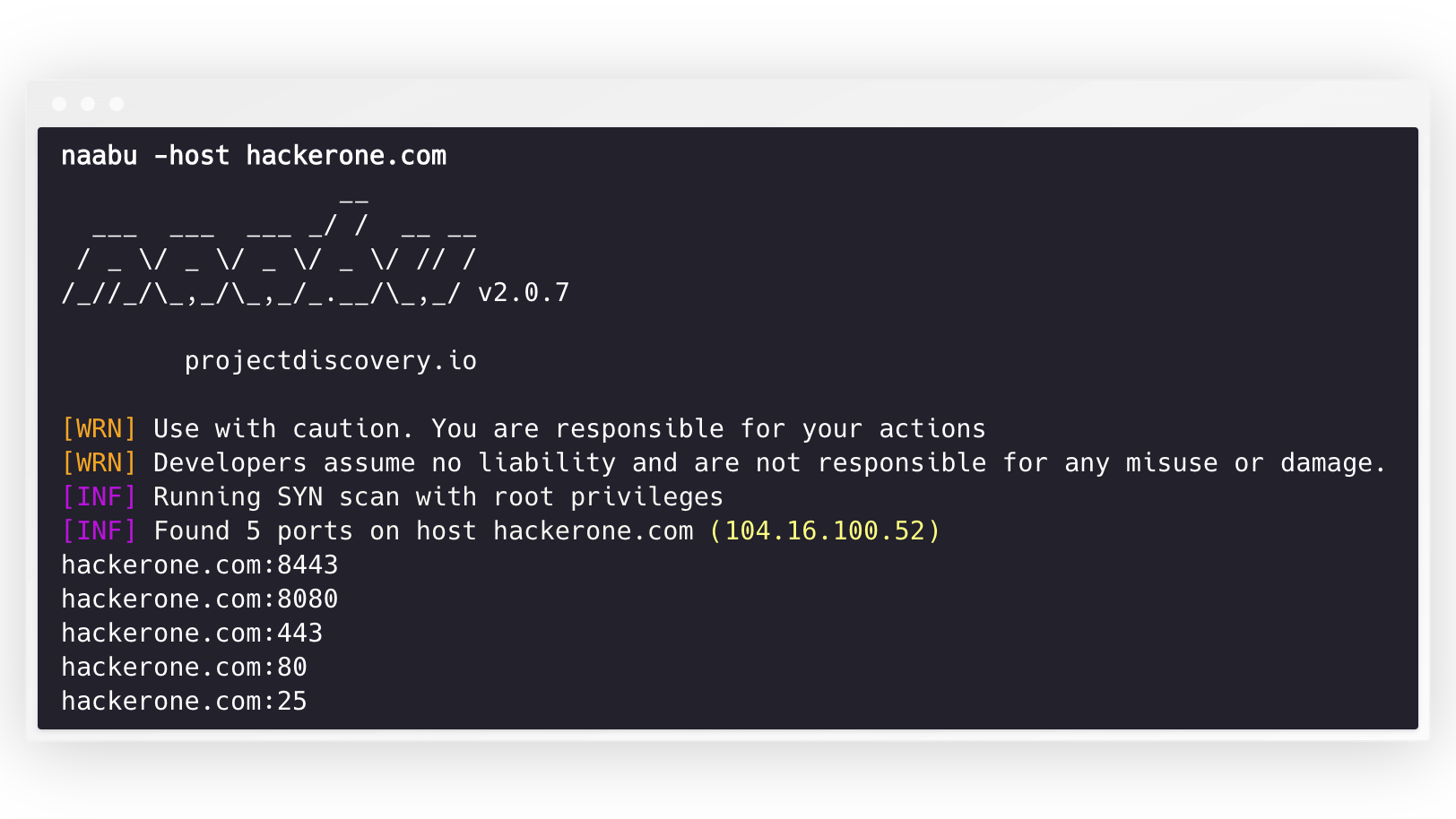
naabu -host hackerone.com这将针对Hackerone.com运行该工具。有许多配置选项,您可以与此命令一起传递。详细开关-v可用于显示详细信息。
naabu -host hackerone.com
__
___ ___ ___ _/ / __ __
/ _ / _ / _ / _ / // /
/_//_/_,_/_,_/_.__/_,_/ v2.0.3
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[INF] Running SYN scan with root privileges
[INF] Found 4 ports on host hackerone.com (104.16.100.52)
hackerone.com:80
hackerone.com:443
hackerone.com:8443
hackerone.com:8080可以在主机上扫描的端口可以通过-p参数指定(UDP端口必须表示为u:port )。它需要NMAP格式端口并在其上运行枚举。
naabu -p 80,443,21-23,u:53 -host hackerone.com默认情况下,NAABU检查了NMAP的Top 100端口。它支持以下内置端口列表 -
| 旗帜 | 描述 |
|---|---|
-top-ports 100 | 扫描NMAP前100个端口 |
-top-ports 1000 | 扫描NMAP顶部1000端口 |
-p - | 从1-65535扫描全端口 |
您还可以指定要从扫描中排除的特定端口。
naabu -p - -exclude-ports 80,443为了在主机列表中运行Naabu,可以使用-list选项。
naabu -list hosts.txt要在ASN上运行Naabu,因为可以使用输入。它采用给定ASN的IP地址,并在其上运行枚举。
echo AS14421 | naabu -p 80,443
216.101.17.249:80
216.101.17.249:443
216.101.17.248:443
216.101.17.252:443
216.101.17.251:80
216.101.17.251:443
216.101.17.250:443
216.101.17.250:80您还可以使用-json Switch以JSON格式获取输出。此开关以JSON线格式保存输出。
naabu -host 104.16.99.52 -json
{"ip":"104.16.99.52","port":443}
{"ip":"104.16.99.52","port":80}发现的端口也可以将其管道输送到其他工具。例如,您可以将Naabu发现的端口移至HTTPX,然后在主机上找到运行HTTP服务器。
echo hackerone.com | naabu -silent | httpx -silent
http://hackerone.com:8443
http://hackerone.com:443
http://hackerone.com:8080
http://hackerone.com:80速度可以通过更改代表每秒数据包数量的rate标志的值来控制。在处理宿主时增加它可能会导致假阳性率提高。因此,建议将其保持在合理的数量。
Naabu支持IPv4和IPv6。两个范围都可以作为输入一起管道。如果使用IPv6,则必须正确配置连接性,并且网络接口必须具有分配的IPv6地址( inet6 )和默认网关。
echo hackerone.com | dnsx -resp-only -a -aaaa -silent | naabu -p 80 -silent
104.16.99.52:80
104.16.100.52:80
2606:4700::6810:6434:80
2606:4700::6810:6334:80选项-ip-version 6使该工具在解决域名时使用IPv6地址。
echo hackerone.com | ./naabu -p 80 -ip-version 6
__
___ ___ ___ _/ / __ __
/ _ / _ / _ / _ / // /
/_//_/_,_/_,_/_.__/_,_/ v2.0.8
projectdiscovery.io
Use with caution. You are responsible for your actions
Developers assume no liability and are not responsible for any misuse or damage.
[INF] Running CONNECT scan with non root privileges
[INF] Found 1 ports on host hackerone.com (2606:4700::6810:6334)
hackerone.com:80要扫描这两个版本的所有IP, ip-version 4,6可以与-scan-all-ips标志一起使用。
echo hackerone.com | ./naabu -iv 4,6 -sa -p 80 -silent
[INF] Found 1 ports on host hackerone.com (104.16.100.52)
hackerone.com:80
[INF] Found 1 ports on host hackerone.com (104.16.99.52)
hackerone.com:80
[INF] Found 1 ports on host hackerone.com (2606:4700::6810:6334)
hackerone.com:80
[INF] Found 1 ports on host hackerone.com (2606:4700::6810:6434)
hackerone.com:80Naabu(可选)支持多个执行主机发现的选项。主机发现是可选的,可以使用-wn标志启用。 -sn标志指示该工具仅执行主机发现。
可用的可执行主机发现的选项:
-arp )-ps 80 )-pa 443 )-pe )-pp )-pm )-nd )Naabu支持配置文件默认位于$HOME/.config/naabu/config.yaml ,它允许您定义配置文件中的任何标志,并设置默认值以包含所有扫描。
我们已经集成了NMAP支持服务发现或NMAP支持Naabu结果支持的任何其他扫描,请确保已安装nmap来使用此功能。
为了使用,可以使用NMAP命令使用nmap-cli标志,例如: -
echo hackerone.com | naabu -nmap-cli 'nmap -sV -oX nmap-output'
__
___ ___ ___ _/ / __ __
/ _ / _ / _ / _ / // /
/_//_/_,_/_,_/_.__/_,_/ v2.0.0
projectdiscovery.io
[WRN] Use with caution. You are responsible for your actions
[WRN] Developers assume no liability and are not responsible for any misuse or damage.
[INF] Running TCP/ICMP/SYN scan with root privileges
[INF] Found 4 ports on host hackerone.com (104.16.99.52)
hackerone.com:443
hackerone.com:80
hackerone.com:8443
hackerone.com:8080
[INF] Running nmap command: nmap -sV -p 80,8443,8080,443 104.16.99.52
Starting Nmap 7.01 ( https://nmap.org ) at 2020-09-23 05:02 UTC
Nmap scan report for 104.16.99.52
Host is up (0.0021s latency).
PORT STATE SERVICE VERSION
80/tcp open http cloudflare
443/tcp open ssl/https cloudflare
8080/tcp open http-proxy cloudflare
8443/tcp open ssl/https-alt cloudflareNaabu还支持排除扫描端口的CDN/WAF IPS。如果使用,只有80和443端口被扫描到那些IPS。可以使用exclude-cdn标志启用此功能。
目前, cloudflare , akamai , incapsula和sucuri IPs被支持。
Naabu在http://localhost:63636/metrics (可以通过-metrics-port flag更改端口)上,曝光JSON扫描信息:http:// localhost:63636/量表
以下示例程序扫描scanme.sh的80端口。结果通过OnResult回调返回:
package main
import (
"log"
"github.com/projectdiscovery/goflags"
"github.com/projectdiscovery/naabu/v2/pkg/result"
"github.com/projectdiscovery/naabu/v2/pkg/runner"
)
func main () {
options := runner. Options {
Host : goflags. StringSlice { "scanme.sh" },
ScanType : "s" ,
OnResult : func ( hr * result. HostResult ) {
log . Println ( hr . Host , hr . Ports )
},
Ports : "80" ,
}
naabuRunner , err := runner . NewRunner ( & options )
if err != nil {
log . Fatal ( err )
}
defer naabuRunner . Close ()
naabuRunner . RunEnumeration ()
}Naabu是由?由Project Discovery团队。社区贡献使该项目的本质成为现实。
有关更多详细信息,请参见Thyny.md文件。