PE-Packer is a simple packer for Windows PE files. The new PE file after packing can obstruct the process of reverse engineering.
It will do the following things when packing a PE file:
When running a packed PE file, the shell-entry will decrypt and load the original program as follows:
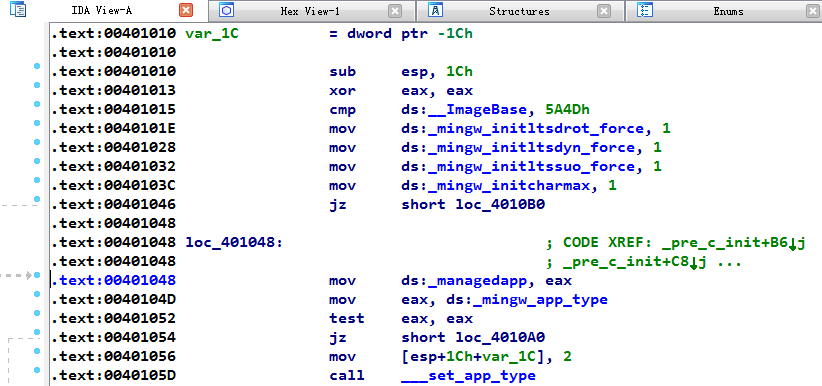
Before packing, using some disassembly tools can disassemble the executable file to analyze the code, such as IDA Pro.
Disassembling the code.
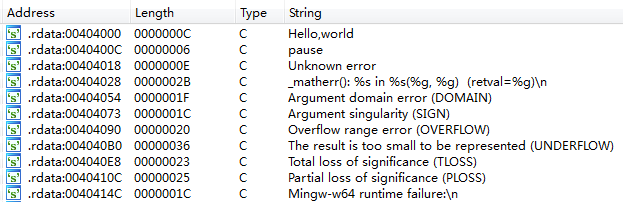
Searching constant strings.
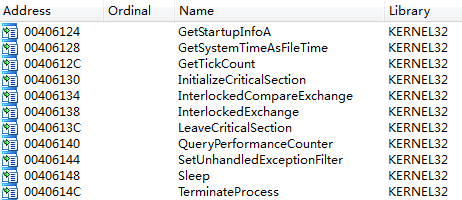
Analyzing the import table.
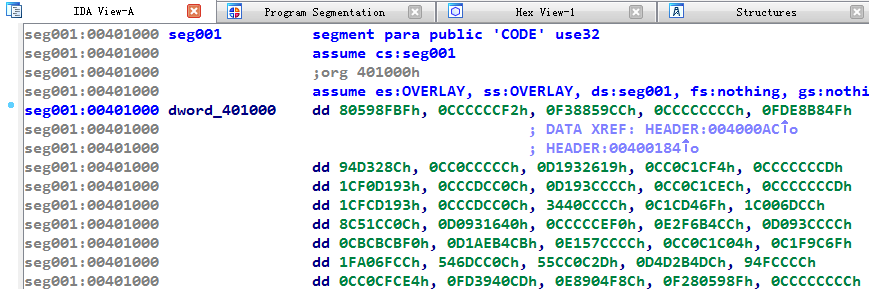
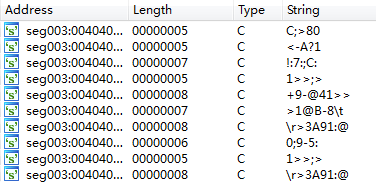
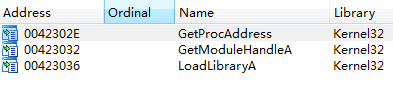
After packing, the reverse analysis will be obstructed.
Disassembling the code.
Searching constant strings.
Analyzing the import table.
This project is just a demo for beginners to study Windows PE Format and Assembly Language. It still has some compatibility problems and bugs that cannot be used in practice.
The project must configure on/for Windows 32-bit and can only process 32-bit .exe programs now.
i686 architecture.PATH environment variables of these three tools.mkdir -p build
cd build
cmake .. -D CMAKE_C_COMPILER=gcc -G "MinGW Makefiles"
cmake --build .Or run the build.ps1 file directly:
PS> .build.ps1To pack a program, you must specify its input name and the output name.
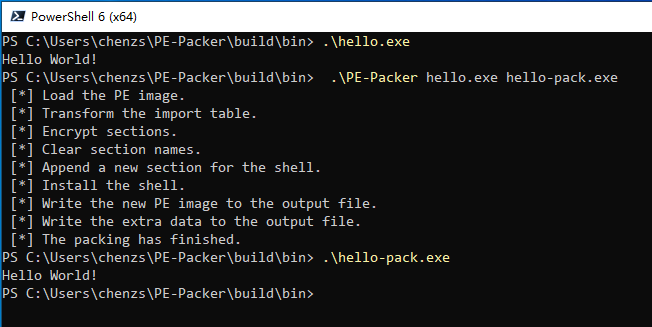
PE-Packer <input-file> <output-file>For example:
PE-Packer hello.exe hello-pack.exeYou can use Doxygen to generate the document.
Distributed under the MIT License. See LICENSE for more information.